Secure Data in Transit
All information exchanged between Graphio, customers, and external services is protected using TLS 1.2/1.3 encryption. This ensures that sensitive data cannot be intercepted or altered during transmission.
We prioritize security, privacy, and transparency at every level of our product and operations.
Our platform is built to exceed industry standards like SOC 2 Type 2, HIPAA, GDPR, and CCPA – so your data stays protected and compliant.
Protecting all data in motion with secure, encrypted communication across every connection.
All information exchanged between Graphio, customers, and external services is protected using TLS 1.2/1.3 encryption. This ensures that sensitive data cannot be intercepted or altered during transmission.

Every internal microservice within Graphio’s infrastructure communicates via encrypted TLS/SSL channels, eliminating exposure of sensitive data inside private networks.
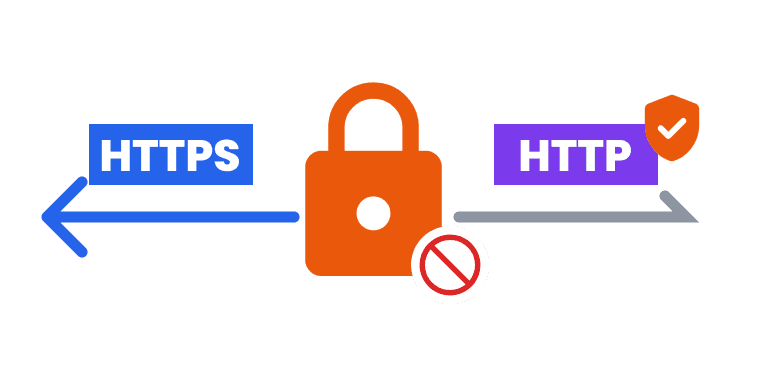
Graphio APIs and web interfaces enforce HTTPS-only access, blocking any unsecured HTTP requests to prevent man-in-the-middle or downgrade attacks.
Graphio processes only metadata — such as timestamps, source identifiers, and event categories — without ever accessing or analyzing the actual content of messages, files, or emails.
Raw data obtained from external APIs (Slack, Jira, HubSpot, Google Workspace, QuickBooks, and others) is used solely to generate metadata packets, which are immediately processed and securely deleted after completion.
All internal services and employees operate under the least-privilege access model, ensuring that every component and user has only the minimal permissions required to perform its function.
Data processing complies with Data Processing Addendum (DPA) and Standard Contractual Clauses (SCC), ensuring full legal protection for international data transfers and enterprise clients.
Encrypted, isolated data storage with continuous monitoring and protection.

All information exchanged between Graphio, customers, and external services is protected using TLS 1.2/1.3 encryption. This ensures that sensitive data cannot be intercepted or altered during transmission.

Every internal microservice within Graphio’s infrastructure communicates via encrypted TLS/SSL channels, eliminating exposure of sensitive data inside private networks.

Backups are encrypted and stored separately in restricted-access environments, isolated from production systems. Access to backup data is limited to senior security administrators under strict audit control.

Graphio conducts periodic penetration tests and vulnerability assessments to identify potential weaknesses in its storage and encryption mechanisms.
Graphio’s security controls are independently audited under the SOC 2 Type 2 framework, covering operational effectiveness of data protection, confidentiality, and availability controls.
Our systems meet HIPAA security and privacy rules, ensuring protection for health-related data when applicable.
Graphio is compliant with EU General Data Protection Regulation (GDPR) and California Consumer Privacy Act (CCPA), enabling full transparency and user control over personal data. Users can request data deletion or export at any time.
We maintain and sign Data Processing Agreements (DPAs) and Standard Contractual Clauses (SCCs) with all enterprise clients and subprocessors to ensure legal compliance for international data transfers.
Graphio’s infrastructure operates under a Zero Trust Architecture, where no device, user, or service is implicitly trusted. Every request is continuously verified for identity, context, and permissions.
Access rights within the platform are governed by granular RBAC policies, ensuring that only authorized personnel can view or modify specific systems, data, or configurations.
All administrative and API-level actions are logged into a centralized audit system (Graylog). Logs are analyzed in real time to detect anomalies, intrusion attempts, or unauthorized actions.
Employee and service authentication is enforced via Single Sign-On (SSO) integrated with Google Workspace and Microsoft Azure Active Directory. This minimizes credential-based risks and simplifies compliance auditing.
Infrastructure components are continuously patched and updated to maintain the latest security posture in line with industry best practices and CVE vulnerability lists.
Minimal retention, secure disposal, full customer control of stored data.

Temporary data, cache, and logs are retained for no longer than 30 days and then automatically purged from all systems.

Users can revoke access and delete all stored data by removing the Graphio integration from connected systems such as Google Workspace, Slack, HubSpot, etc.

All encrypted backups are automatically destroyed upon expiration of their retention window, preventing residual data recovery.

Graphio provides clear interfaces and documentation for customers to manage, audit, and erase their data at any time in compliance with GDPR Article 17 (“Right to be Forgotten”).
Implementing Graphio takes only a few days. The onboarding process follows secure deployment and authentication standards to ensure compliance from the first connection.
All integrations are plug-and-play — requiring no engineering effort, code deployment, or manual key exchange. This minimizes security risks during setup.
Every integration (Slack, HubSpot, Jira, Google Workspace, QuickBooks, etc.) passes Graphio’s internal security and privacy review before being enabled in production environments.
The platform continuously monitors integration states and permissions, alerting administrators if scopes or security settings change.